Broken Object Level Authorization, The Quiet API Flaw Behind Million User Breaches
When identifiers become keys, your entire system can quietly fall apart.
Why It’s Important
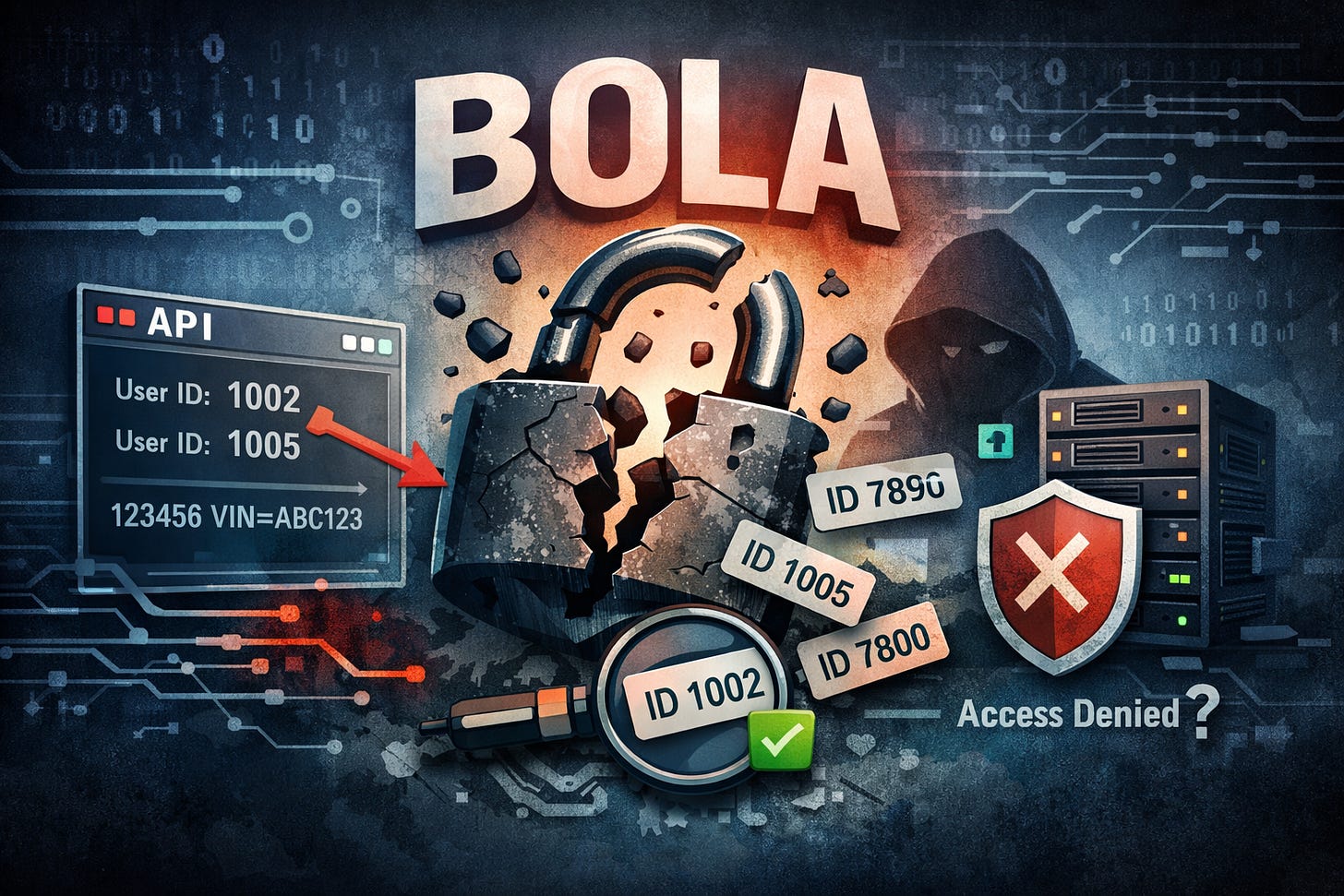
Broken Object Level Authorization, often called BOLA, is not just another entry on the OWASP Top 10 list. It has become one of the most common and damaging API vulnerabilities in modern applications.
APIs now power banking apps, connected vehicles, social platforms, cloud tools, and telecom portals. When object level authorization is not properly enforced, attackers do not need sophisticated malware. They simply change an ID number in a request and gain access to data that does not belong to them.
The impact is severe. Financial transactions can be manipulated. Private user data can be scraped at scale. Service histories, account records, and internal exports can be downloaded without permission.
And here is the uncomfortable truth. Many security teams still focus on authentication, meaning who you are, while missing authorization, meaning what you are allowed to access.
BOLA exploits that blind spot.
What It Is and How It Works
To understand BOLA, picture an apartment building.
Authentication is the front door. You prove you live in the building. Authorization is the lock on your individual apartment.
If the building checks your identity at the entrance but allows you to open any apartment door once inside, you have a Broken Object Level Authorization problem.
In technical terms, BOLA happens when:
A user is properly authenticated.
The application exposes object identifiers, such as user IDs, account numbers, VINs, or export job IDs.
The server fails to verify whether the authenticated user is allowed to access that specific object.
The system assumes that because the request is authenticated, it must also be authorized.
Modern APIs make this worse because they rely heavily on predictable identifiers:
User IDs like 1001, 1002, 1003
Vehicle VIN numbers
Transaction IDs
File export job IDs
Customer account numbers
If the backend does not check ownership or permissions for each object request, changing that identifier becomes an access bypass.
Now let’s look at how this played out in real incidents.
Real World Breaches Where BOLA Was the Root Cause
Volkswagen 2025
In 2025, connected car APIs reportedly exposed owner data and service histories using nothing more than a VIN. A VIN is physically visible on every vehicle. It was treated as a trusted lookup key.
The issue was not authentication alone. It was the assumption that possession of a VIN equaled authorization. Telematics systems increasingly rely on APIs, and when identifiers double as authorization tokens, privacy collapses.
This case shows how Internet of Things ecosystems amplify BOLA risks. Physical identifiers become digital keys.
Peloton 2021
Peloton fixed an API vulnerability that allowed unauthorized access to user profile data by manipulating user IDs. Even users with private profiles were exposed because the backend failed to enforce object level authorization consistently.
What makes this case important is the false sense of safety around login walls. Many assume that once authentication is required, the system is secure. But this was a horizontal authorization flaw. Attackers did not need admin privileges. They only needed to change a user identifier.
This is a powerful reminder that authentication is not the same as authorization.
Experian 2021
An API connected to credit score services could be queried using basic personal information. Under certain conditions, the endpoint failed to properly enforce authorization controls before returning sensitive financial data.
Credit data is among the most sensitive personal information in existence. When object level checks are weak in identity systems, the impact extends beyond privacy into fraud and identity theft.
This case illustrates how BOLA is especially dangerous in high trust environments where personal identifiers are treated as sufficient proof of access rights.
Optus 2022
An unauthenticated API endpoint exposed customer data when attackers modified identifiers within requests. Personal information including identification numbers was accessible without proper authorization enforcement.
Telecom providers store enormous volumes of personal data. Lookup APIs that retrieve account records are frequent targets because they often rely on predictable identifiers and insufficient access validation.
The Optus incident reinforces a consistent pattern seen in other telecom breaches. When object level authorization is missing, enumeration becomes trivial.
Coinbase 2022
A flaw in a trading API allowed unauthorized trades under certain conditions. This demonstrates how BOLA does not just expose data. It can enable state changing operations.
When object level authorization fails in financial systems, the impact goes beyond privacy. It affects integrity. Unauthorized trades, balance manipulation, or transaction triggers become possible.
In high risk environments like cryptocurrency exchanges, BOLA can directly translate into financial loss.
Instagram 2019
Predictable user IDs combined with missing authorization checks allowed large scale scraping of private user data.
Here is the subtle bias many teams carry. If a user is logged in, they assume access to adjacent records is harmless. But BOLA does not require privilege escalation. It only requires horizontal access.
Attackers iterated through user IDs and harvested data in bulk. This turned a small logic flaw into a mass privacy issue.
T-Mobile 2023
An unauthenticated API exposed data from 37 million customer accounts. Lookup endpoints that returned account data lacked proper object level authorization.
This example highlights another misconception. Some teams believe that read only endpoints are low risk. In reality, data exposure is often the primary objective of attackers.
Across all these cases, the pattern is consistent. The system trusted the client request instead of validating access server side for every object.
Why Traditional Security Reviews Miss BOLA
There is a structural bias in many development teams.
They focus on perimeter defenses, input validation, and authentication flows. They assume that once a user is logged in, access patterns are predictable.
But BOLA hides in business logic.
Automated scanners often fail to detect it because the API behaves normally. The flaw appears only when object identifiers are modified in specific ways.
Security reviews that rely on static checklists instead of dynamic testing miss the nuance.
Frameworks such as National Institute of Standards and Technology guidance in the NIST SP 800 series and standards like ISO 27001 emphasize access control policies. However, policy documentation does not guarantee enforcement at the object level inside APIs.
BOLA is an implementation failure, not just a policy gap.
How To Mitigate It
Reducing BOLA risk requires disciplined server side enforcement.
First, enforce authorization checks on every object request. Every API endpoint that retrieves, modifies, or deletes data must validate ownership or permissions.
Second, avoid predictable identifiers where possible. While not a primary fix, using non sequential IDs reduces trivial enumeration.
Third, implement centralized authorization logic. Do not scatter permission checks across microservices inconsistently.
Fourth, use automated API security testing tools that simulate object ID manipulation.
Fifth, log and monitor abnormal object access patterns. Rapid sequential access to multiple object IDs is often a red flag.
Most importantly, design with the mindset that clients are untrusted. Even internal applications can be manipulated.
How To Implement Strong Object Level Authorization
For development teams, practical steps include:
Use role based or attribute based access control. Attribute based models check contextual data such as ownership, department, or subscription level.
Validate object ownership directly in database queries. For example, include user ID constraints in the data retrieval logic rather than checking after data is fetched.
Perform code reviews specifically focused on API object access patterns.
Map endpoints against the OWASP API Security Top 10 to ensure BOLA is addressed explicitly.
For organizations aligning with regulatory requirements such as General Data Protection Regulation, object level authorization is not optional. Exposure of personal data through weak access controls can trigger serious penalties.
One Capability I Appreciate in Modern API Gateways
One capability I consistently value is centralized policy enforcement at the API gateway layer.
When authorization logic is handled in a unified layer rather than scattered across services, it becomes easier to audit and test. It also reduces human error. Developers can focus on business logic while the gateway verifies whether a requestor should access a specific object.
This approach does not eliminate the need for backend validation, but it creates an additional control point that strengthens security.
☕Want to support my work? Consider buying me a coffee
A Smart Tool To Strengthen Your Digital Identity
While BOLA is primarily a developer concern, users are not powerless.
I recommend using a privacy focused VPN with built in tracker blocking such as Proton VPN. Beyond masking IP addresses, it helps reduce data correlation and limits exposure when interacting with web services that may have poorly designed APIs.
Reducing your digital footprint makes large scale scraping efforts less profitable.
The Bigger Lesson
BOLA teaches a simple but powerful lesson. Authentication answers who you are. Authorization answers what you are allowed to touch.
Confusing the two creates silent systemic risk.
As APIs continue to power finance, vehicles, healthcare, and social platforms, object level authorization must be treated as a first class security requirement, not an afterthought.
If you are a developer, review your endpoints this week. If you are a security leader, ask your team how object access is validated across services.
Because in modern systems, an ID is never just an ID.
What would happen if someone incremented an object ID inside your most sensitive API today?